You’ve probably heard of phishing, where scammers try to get private personal information via email or text. Cyber thieves also use “vishing,” a combination of “voice” and “phishing” that is conducted not only through incoming phone calls but through a button or link you can click on your computer.
It’s becoming increasingly common, representing 30% of all incoming mobile calls. Once the hackers have tricked you into installing malware, your computer is infected, and they have access to all those personal files you thought were gone but hadn’t been permanently deleted. It’s a double whammy because they also have your credit card information. This guide will walk you through what successful vishing does and how you can protect yourself and your personal data.
How Vishing Works
With phishing, you click on an email or text link. Vishing involves a live human being who works a verbal scam to trick you into doing something you think is in your best interests.
The usual scenario is that you get a call from a person pretending to be from a company you trust, such as your bank. They might ask for your bank site login info and use it to access your accounts. You might also visit a website, and up pops a message of a serious problem with your computer. It urges you to call a technician immediately, and the person who answers tells you they can help by installing a piece of software on your computer, but for a price.
Or, let’s say you’re on a social media site, for example, and you see an interesting ad. When you click the link, embedded malware locks up your computer, and the only way it can be fixed, according to the message that pops up, is to call a phone number to speak with a technician. The so-called technician asks for your credit card number to pay for the repair. That means the scammers have access not only to your private files but also to your credit card. They might also send you a link by email or text message to install their malware on your device that could cause any number of issues, none of them good.
The Costs of Vishing Attacks
Vishing is so common that the FBI has issued a warning about the threat. These criminals are targeting employees’ computers using social engineering techniques. That term refers to using tricks and emotional manipulation to cause their targets to allow access to their devices, credentials, and financial information.
The financial price of vishing is enormous: In 2018, the cost to victims was $48 million. Money, however, is not the only cost of a vishing-related data breach. The intangible costs, which are critical to company performance, can include:
Business Interruption
A business victimized by vishing is thrown into a survival posture that consumes everyone’s time for weeks or months. Everything is delayed, including product launches, new marketing campaigns, and IT initiatives. Often the security team will need time to investigate, contain the risks as much as possible, and implement a recovery plan.
Loss of Clients’ Trust
You may have thought passwords and other security measures protected you, and you dragged those old client files into the computer trash and deleted them. Unless you’ve permanently deleted those files, though, they can be recovered by cyber thieves. Affected customers are likely to take their business to a company that will take better care of their information.
Reputational Damage
A vishing attack can ruin your reputation with vendors who don’t want to work with a company that had a data breach. It can even affect your ability to get emails into the inboxes of those you’re trying to reach, as some services will block you after a security incident.
Vishing came into its own in 2020. It became increasingly sophisticated and targeted all those employees working from home. With these attacks on the rise and so much at risk, it’s essential to protect your data.

6 Tips to Protect Yourself From Vishing
Understanding the basics of vishing is only the first step. Knowing how to protect yourself is vitally important, and the FBI and cybersecurity specialists recommend these additional measures to safeguard your data:
1. Use Multifactor Authentication
This is a crucial step to mitigate the chances of a scammer accessing employee accounts. It requires a second form of verification, such as a code sent to your phone, before anyone can log in to a website.
2. Be Careful With Network Access
Review network access for all employees to reduce the risk of compromise and reveal vulnerabilities in your network. When you hire a new employee, grant access based on a “least privilege” basis, enabling them to use only what they need to do their job.
3. Actively Scan Your Network and Break It Into Segments
You can prevent or minimize the loss of any data via vishing by monitoring for unauthorized access or any access modifications. If you have a large network, break it up into smaller segments that are easier to monitor and control traffic flow.
4. Issue Two Accounts to Administrators
Administrators should have one account with the privilege to make changes to the system and another account for generating reports and managing emails and updates.
5. Before You Call, Verify
You should verify any phone number in an email or pop-up message before calling it. It’s wise to contact your bank’s published customer service line if you get a message to call the bank, not the number the message gave you. You should also refuse any requests for your login info; a real company will already have that and wouldn’t need to ask.
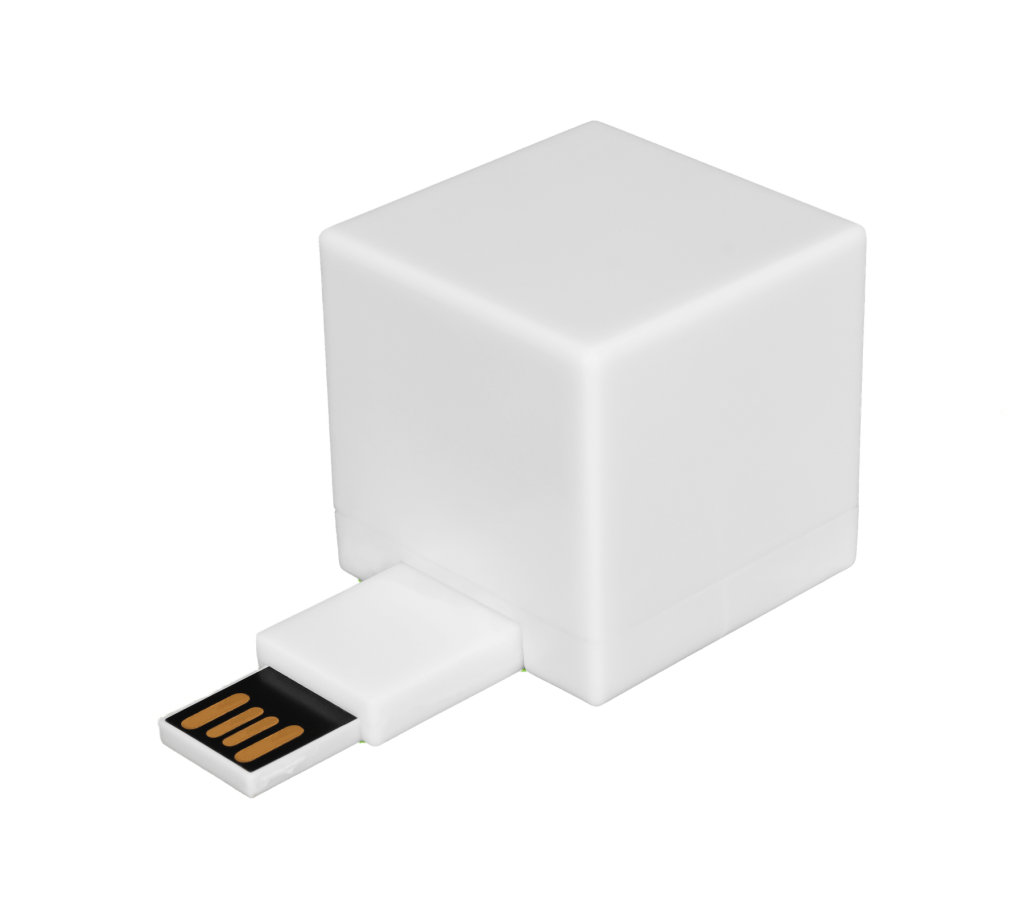
6. Securely Destroy Sensitive Data
Your computer’s trash bin is far from secure, and those files are not really gone. A simple web search shows dozens of companies that can help you recover those files. Make sure personal, client, legal, financial, and other sensitive information is really erased – permanently – by using a digital file shredder.
Avoiding vishing attacks means being suspicious of anyone who asks you for login information over the phone, wants account data or personal information, or pretends to represent a security firm or government agency like the IRS or Social Security. These organizations won’t ever make these requests over the phone, so hang up.
The U.S. government also has a website for reporting scams and frauds, with helpful links.
Contact the Experts in Permanent File Erasure and Reduce Vishing Risks
With vishing and other cyberattacks on the rise, it’s never been more important to have the right resources to protect yourself and your data. Emptying your computer’s trash can is not enough–you need a solution that deletes those sensitive files permanently. The Shred Cube provides an all-new way to destroy data by permanently deleting unwanted documents or files, which are often targeted by cybercriminals. Simple features such as drag-and-drop, file attachment, duplicate file finder and more ensure that privacy is now just a click away. Get in touch today to learn about the first and only USB file shredder.